
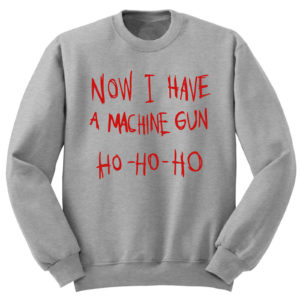
It’s that time of year where many of us will be ensuring our organisations can still deal with a security incident whilst most of the workforce are at home watching Christmas movies like Die Hard – yes, it’s definitely a Christmas Movie. Hackers know businesses are running on skeleton staff during the holiday period so it’s critical that organisations of all shapes and sizes put in place some simple precautions to minimise the chances of a service disruption or a data breach. Here are some simple things businesses can put in place so employees can spend more time enjoying time with their family and less time recovering from a seasonal ransomware attack!
Security Incident Avoidance – Don’t put security changes in a deep freeze!
One of the biggest (if not the biggest) sources of technology disruption is change. Most organisations recognise this and implement change freezes during the Christmas period because not only are internal IT departments typically under-staffed during this time but so too are vendor third line support teams. That said, there is no getting around the fact that sometimes change is still required, even during a change freeze. It could also be argued that the period which may be quiet for other parts of the business could be the perfect time to get a lot of the housekeeping tasks done which have been kicked into the long-grass during the course of the year.
Security Incident Avoidance – Fix those servers on the naughty list!
Expanding on the first point, InfoSec and IT should work together to identify security changes which could be implemented with minimal impact to the business and customers during the wider change freeze. Run a wide-ranging vulnerability scan across the network, check your servers against the CIS hardening standards (or your own hardening standards if they exist). Identify candidates for quick wins (e.g. removing insecure encryption algorithm, installing LAPS, implement 2FA for Admins).
Security Incident Avoidance – Check you can contact all your elves!
There are two kinds of elves in this scenario. The first being your human elves i.e. those you may need to contact in an emergency. Check you have the most up-to-date contact details for your incident management team and your senior management team. Physically call them. DO NOT rely on any internal phone directories or email signature blocks (which may not have been updated or may just contain their desk number). Make sure you let people know they need to be contactable during an incident and agree on what decisions can be delegated if someone is incommunicado during a major incident. The second types of elves are your servers and network infrastructure…
Does it SIEM too quiet?
Whilst we’re entering into 2020 it is still commonplace for organisations to not have a SIEM. In some cases, the raw logging capability isn’t even turned on, and where it is turned on, it’s not actively monitored. By not logging you are seriously hampering the ability to detect, respond and recover from a security incident I cannot stress this enough but:
TURN CENTRALISE LOGGING ON!!!
Even if you don’t actively monitor the logs it’s still better to have centralised logging turned on than disabling what is an incredibly rich source of forensic information about your network. These days it’s not even that hard to do.
For those who have moved up the maturity curve make sure your logs are still being shipped your central logging server by setting up alerting mechanisms. Don’t just stop there, test that the alerting will work in different circumstances. Will you still get alerts that logging is functioning if your email gateway goes down for example?
Yippee Ki- yay
If you do experience a Nakatomi Plaza incident of your own, a security incident can be very stressful. Whilst your SOC team hopefully won’t have to run barefoot across broken glass they will be put under a significant amount of pressure to get things up and running as soon as possible. Help them by removing easily avoidable disruption. Implementing these few simple measures will significantly reduce the chances of a Nightmare before Christmas…let’s not give Hans the Hacker an open goal.
About The Author
About Fox Red Risk
Fox Red Risk is a boutique data protection and cybersecurity consultancy and Managed Security Service Provider which, amongst other things, helps client organisations with implementing control frameworks for resilience, data protection and information security risk management. Call us on 020 8242 6047 or contact us via the website to discuss your needs.
22301 22301:2019 application security article 28 awareness bcms BIA business continuity calculating risk change management ciso cybersecurity data breach data privacy Data Protection data protection by design data protection officer data protection service Data Subject Access Request DPO DSAR GDPR incident management information security key risk indicators monitoring operational resilience Outsourced DPO Privacy risk risk appetite risk management ROI security security as a service security awareness small business strategic strategy Subject Access Request tools training vciso vendor risk virtual ciso

